|
February 16—
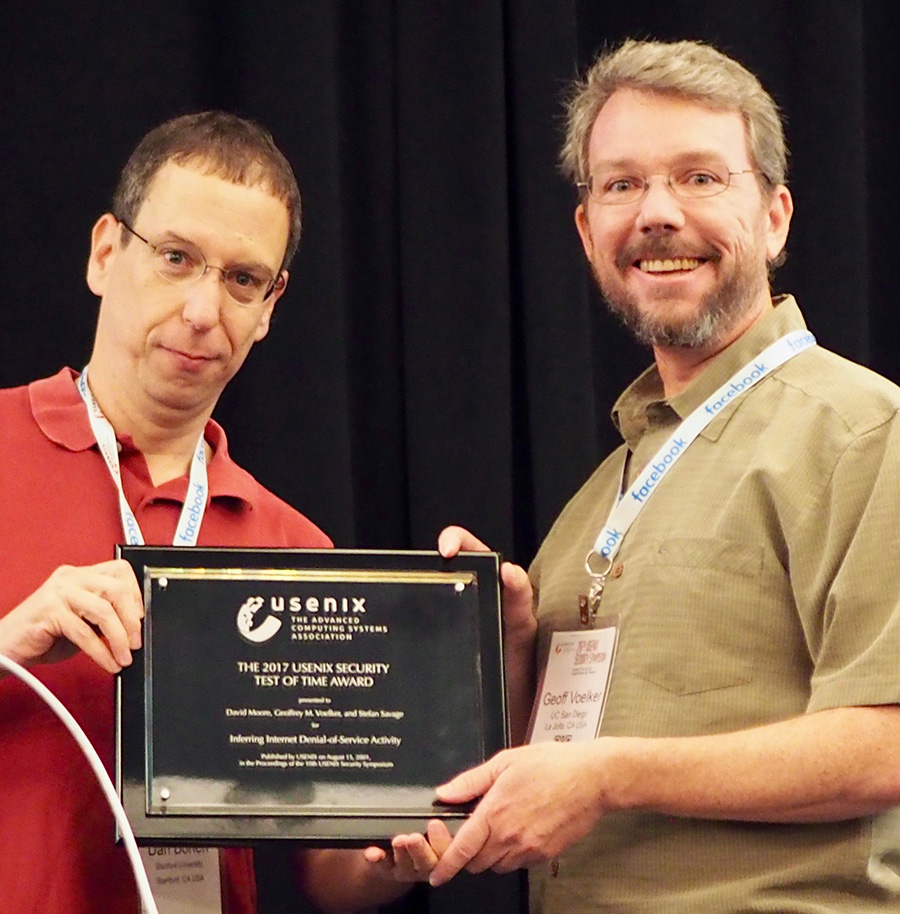
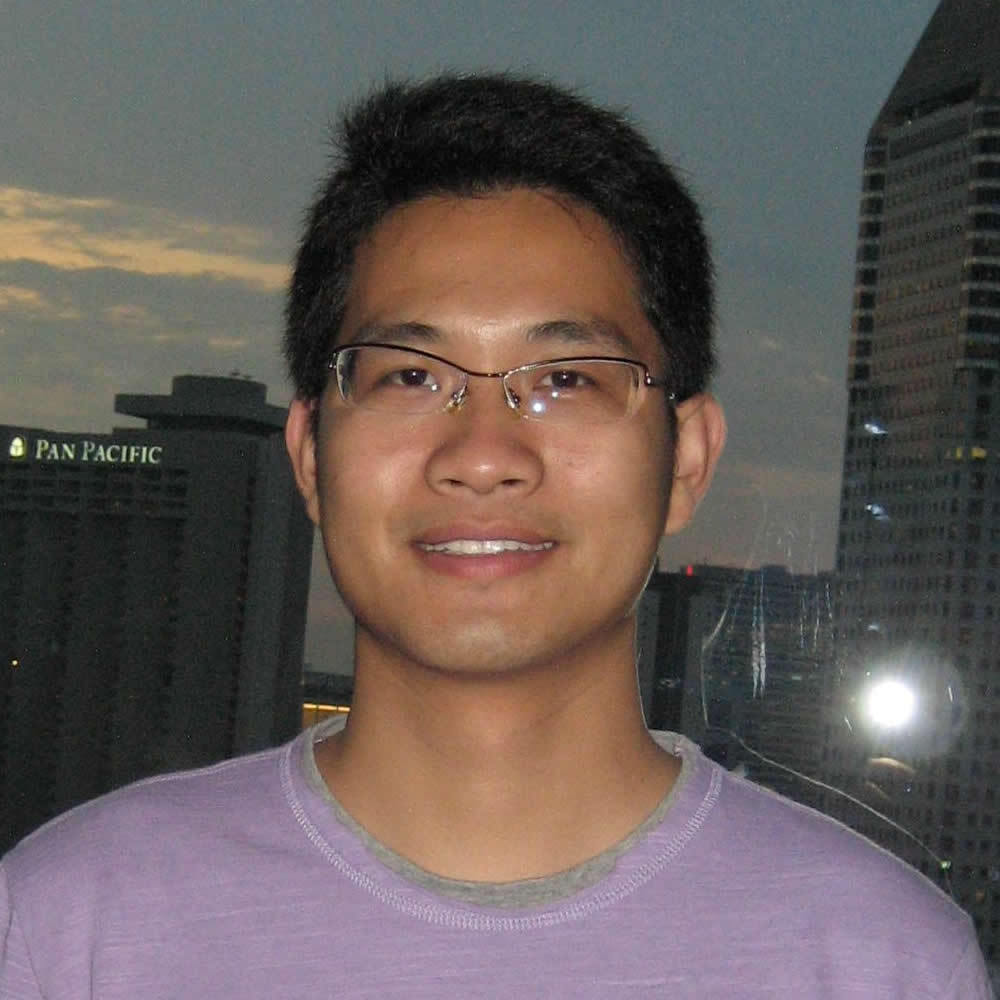
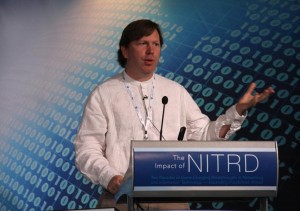
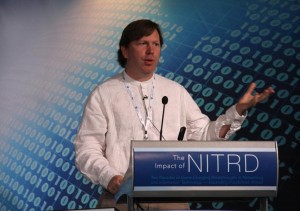
Today, the CCC sponsored a symposium to recognize the 20th anniversary
of the Federal Networking and Information Technology Research and
Development program (NITRD) — the multi-agency funding program
that has sponsored US computing research over the past two
decades. The NITRD
Symposium featured a broad range of technical speakers including
Jeannette Wing, Kevin Knight, Beth Mynatt, Helen Nissenbaum, Sebastian
Thrun, Shwetak Patel, Erik Brynjolfsson, Tom Lange, Vint Cerf, Bill
Scherlis, Russ Altman, David Keyes, Kathy Yelick, Tom Davis, Eric
Brown, Eric Horvitz, Alex Szalay, Tom Kalil, Peter Lee, Chuck Vest and
our own Stefan Savage. In 15 minutes apiece, each
highlighted how transformative twenty years of computing research in
their field has been on the real world.
|
|